Screenshots can be a quick way to accurately report on a technical issue.
Instructions:
Gmail mailboxes can be shared with other users by delegating account access. Typical usages for this would be when you want someone to manage your emails while you’re on vacation, or providing access to a general purpose mailbox to several people. Google refers to this type of access as a delegated account.
The user owning the mailbox has to grant (and remove) access. The setting is located:
Gmail settings > Accounts and Import > Grant access to your account > Add another account
When providing access, you’ll need to decide on two options:
After granting access, the user receiving access has to accept an email invitation to monitor the delegated mailbox. Once the user has accepted the access invitation, it can take up to 30 minutes before the access is finally granted (available).
Once the user has permission to the delegated mailbox, they can access the mailbox from their account menu (upper right corner of the gmail window):
Gmail account icon > select delegated account
This will open a new tab with the delegated mailbox. The user can then perform email tasks as if it was their own account.
The mailbox owner can revoke access. The setting is the same as granting access:
Gmail settings > Accounts and Import > Grant access to your account
A list of users with account access will be listed. Simply remove accounts to revoke their access.
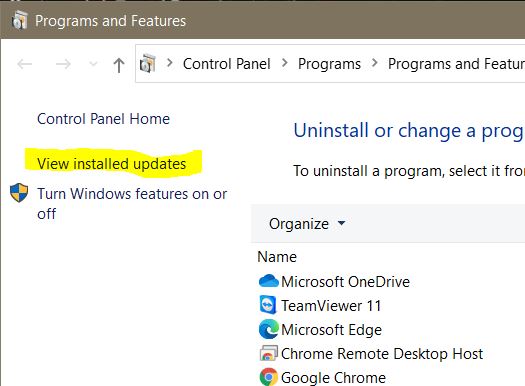
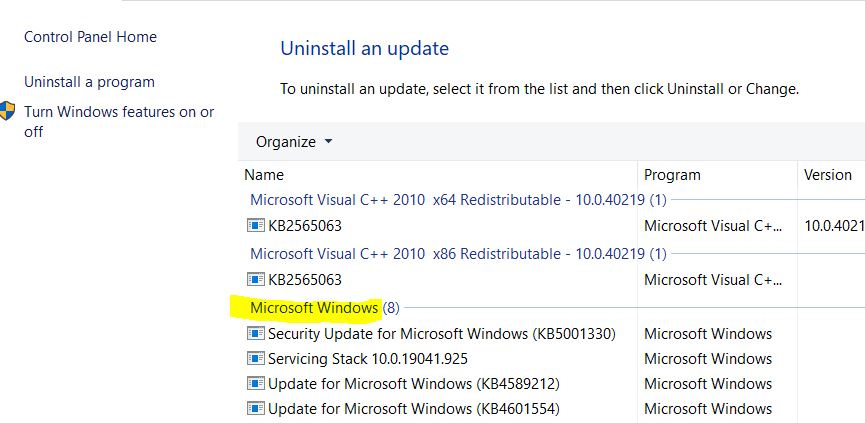
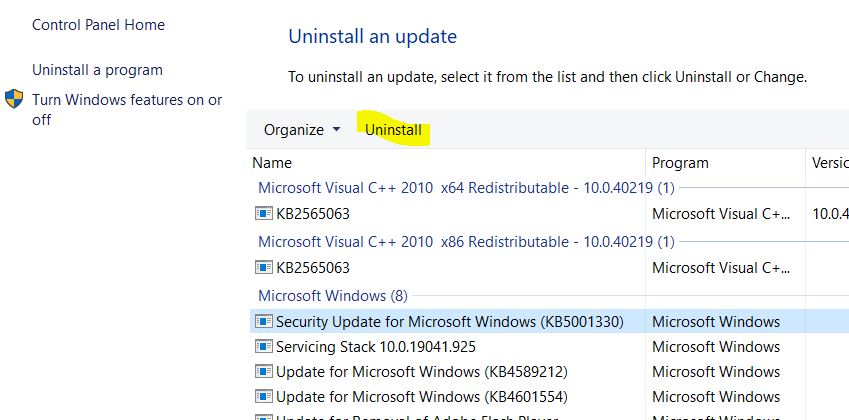
From time to time, Microsoft may release a Windows patch that causes issues with parts of operating system (printing, connectivity, stability issues). And to resolve those issues in a timely fashion, the patch may need to be rolled back (removed).
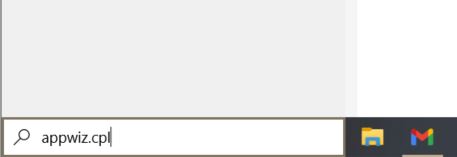
Steps for Removing A Windows Update Patch
 With hundreds of accounts spread across the Internet, covering everything from social media to email to financial data, its important to have strong, unique passwords for every website. But keeping track of those passwords is a huge pain. Many people resort to storing their passwords on paper or a worse, in a document stored on a computer.
With hundreds of accounts spread across the Internet, covering everything from social media to email to financial data, its important to have strong, unique passwords for every website. But keeping track of those passwords is a huge pain. Many people resort to storing their passwords on paper or a worse, in a document stored on a computer.
The best way to deal with all that account security is to use a password management tool. Some of the most popular password management tools:
Things to look for:
Note: Some browsers, like Google Chrome, can do a remarkably good job of generating, storing and recalling passwords. However, that’s about all they can do — that can’t keep track of secret questions, birthdates, etc.
Security tips:
Many households that having been using Apple products, especially iPhones, iPads and the old iPods, share the same iTunes account (now referred to as Apple ID) so that all the family members can have access to the iTunes purchases (music, movies, etc). However, this setup eventually leads to problems with synchronizing information across multiple devices. In particular, contacts get shared with everyone, messages/texts may be randomly delivered, and incoming calls to Facetime will be echoed across all the devices.
The solution to these problems is assign every user their own iCloud account. Some of the additional benefits of having an individual iCloud account include the ability to locate your lost iPhone/Macbook, saving of passwords and backups of photos, etc. This article outlines the steps to provide each user with their own identity, while still allowing purchases in iTunes to be shared.
Like the shared iTunes account, an iCloud account needs to have an email address associated with it. It’s best to use a good long-term email address, not a school or work address. Google provides free email accounts as part of a Google account. Most people use their full name as part of the address, like [email protected] or [email protected]. Make sure you have full access to this email account, as you will receive some verification emails during the iCloud signup.
Create your own iCloud account using that long-term email address.
If you already have your own, unique iCloud account you can skip this step.
On your iPhone/iPad:
On your Macbook:
On your iPhone/iPad:
On your Macbook/iMac:
Make sure you use the same iCloud account on all of your devices (iPhone, iPad, Macbooks, iMacs).
Review your iCloud settings and ensure the following features are turned on:
Also ensure Message is setup on your iPhone:
While using separate Apple accounts for iTunes and iCloud will allow the sharing of iTunes purchases, Apple now has an official sharing program called Family Sharing. It allows one Apple ID to be the primary purchaser, and then shares all the iTunes items like music, movies, apps and Apple Music plans, with up to five family members. It also provides extra services like locating other family members iPhones / Macbooks, family photo albums, and a family calendar (share schedules).
If you decide to switch to Family Sharing, then one person in the family will take over the old Apple ID (iTunes) and use that for their own account. That person will then turn on Family Sharing, and share with the other family members by adding their iCloud accounts. The rest of the family members will switch their iTunes accounts to match their iCloud account.
Internet of Things (IoT) is the latest trend in the Internet saga. IoT is basically the connecting of devices to the Internet for monitoring. Initially, this was simple devices like webcams and smartphones. But now IoT is the monitoring of just about anything. One of the smallest and simplest examples is Amazon’s Dash buttons.  With a single press of the button, the device sends a message back over WIFI to the Amazon motherland, letting them know you want to order more of that product. Other examples include washing machines that let your smartphone know when the current load is done and the Nest thermostat, which observes your heating/cooling usage and adjusts its schedule dynamically, all while tracking and processing much of the information up in the cloud.
With a single press of the button, the device sends a message back over WIFI to the Amazon motherland, letting them know you want to order more of that product. Other examples include washing machines that let your smartphone know when the current load is done and the Nest thermostat, which observes your heating/cooling usage and adjusts its schedule dynamically, all while tracking and processing much of the information up in the cloud.
Looking at a bigger picture, IoT is be used by companies with their products to keep track of inventory and collect information on usage. And all of this data has to be stored and processed somewhere, which is another growth industry.
For most people, one of the biggest and potentially most useful areas of IoT is home automation.  Initially, the process can seem simple: add a WIFI connected thermostat, or a few window and door sensors to detect entry. But the real trick, as with all of IoT, is in the choreography of these devices. With the right home automation setup, the system can warn you when the furnace is turned on but you’ve left a window open and outside temperature will impact the furnace performance. And going deeper, a home automation system can watch for movement within the household after 6 am, and then triggers the turning on of lights (if light levels are detected to be too low), turning up the furnace thermostat, turning off the alarm system, and turning on the coffee maker. The interconnecting of these IoT devices, and the logging and processing of the data, can lead to some complex and powerful systems, which can help not only make your home safer, but save energy and add a lot of convenience.
Initially, the process can seem simple: add a WIFI connected thermostat, or a few window and door sensors to detect entry. But the real trick, as with all of IoT, is in the choreography of these devices. With the right home automation setup, the system can warn you when the furnace is turned on but you’ve left a window open and outside temperature will impact the furnace performance. And going deeper, a home automation system can watch for movement within the household after 6 am, and then triggers the turning on of lights (if light levels are detected to be too low), turning up the furnace thermostat, turning off the alarm system, and turning on the coffee maker. The interconnecting of these IoT devices, and the logging and processing of the data, can lead to some complex and powerful systems, which can help not only make your home safer, but save energy and add a lot of convenience.
However, as of fall 2015, we are still in the early adopter stage. It reminds me a lot of the early days of the personal computers, when there were many producers but the complexity level of assembling and using them was still high. Most early computer users had to build the computer from parts, how to load and run programs from a command line, edit configurations by hand and sometimes even write their own programs. And most people, at the time, thought they would never need a home computer. Most of the advanced home automation systems are much the same way, requiring power users who are comfortable with customizing configurations and loading modules they have to seek out from user forums. And again, most people don’t see all the potential of what these systems can do. There is no clear home automation leader — it is the Wild West still, and one strong horse now could be off the track by next year. Apple, Google, and many more have their fingers in the water, but haven’t produced significant efforts yet.
 One of the early leaders is SmartThings, a kickstarter home automation system that has since been purchased by Samsung. It provides a low cost, fairly open, and highly configurable system that accepts a large number of IoT devices. But it also requires a solid tech understanding of the devices, and frequently custom device type configurations and coding speciality routines. It is one of the most popular systems with the techies, and when working properly, it can do some amazing and complex automation. It’s the TRS-80 of the early IoT days… can it be the IBM PC? As of this writing, the company has been struggling to keep up with their fast growth, and the stability of their product has been suffering.
One of the early leaders is SmartThings, a kickstarter home automation system that has since been purchased by Samsung. It provides a low cost, fairly open, and highly configurable system that accepts a large number of IoT devices. But it also requires a solid tech understanding of the devices, and frequently custom device type configurations and coding speciality routines. It is one of the most popular systems with the techies, and when working properly, it can do some amazing and complex automation. It’s the TRS-80 of the early IoT days… can it be the IBM PC? As of this writing, the company has been struggling to keep up with their fast growth, and the stability of their product has been suffering.
The next few years will see a rapid evolution in IoT, and automation, as these systems become more widespread, and we adapt to more and more technology in our lives.

 The fall of 2013 ushers in a new era in this electronic age, the Smart Watch. These devices bring the comic Dick Tracy wristwatch to reality with the ability to interact with your smart phone, including phone calls, text messaging and app interfaces. Over the next few years we’re sure to see this market boom as the watch design improves. All this leads to an even more integrated electronic connection in our lives. And quite likely, an eventual market reduction in the “old school” watch market.
The fall of 2013 ushers in a new era in this electronic age, the Smart Watch. These devices bring the comic Dick Tracy wristwatch to reality with the ability to interact with your smart phone, including phone calls, text messaging and app interfaces. Over the next few years we’re sure to see this market boom as the watch design improves. All this leads to an even more integrated electronic connection in our lives. And quite likely, an eventual market reduction in the “old school” watch market.
 Smartphones continue to accelerate the merging of technology. As an example, Samsung is planning a camera with the regular point-and-shoot lens, but married with an Android platform. The camera will allow the user to instantly upload and share the photos as well. Calculators, pagers, organizers, planners, GPS units and even cameras have all fallen victim to the rapid development of the smartphone.
Smartphones continue to accelerate the merging of technology. As an example, Samsung is planning a camera with the regular point-and-shoot lens, but married with an Android platform. The camera will allow the user to instantly upload and share the photos as well. Calculators, pagers, organizers, planners, GPS units and even cameras have all fallen victim to the rapid development of the smartphone.
With the passing of Apple’s iconic leader, Steve Jobs, I’ve come to realize how much history I’ve experienced over nearly 35 years with him.
 My first experience with Jobs’ creations was back in high school, when we learned computer programming on the Apple II systems. I was never a big fan of the Apple II , especially their spongy keyboards and strange key placements (I was on the TRS-80 side of the fence), but I did some of my first color computer programming on them. Technology has not always been met with open arms, and I still chuckle remembering the day we came into the computer lab and found someone had stabbed a pencil into the computer, like a dagger.
My first experience with Jobs’ creations was back in high school, when we learned computer programming on the Apple II systems. I was never a big fan of the Apple II , especially their spongy keyboards and strange key placements (I was on the TRS-80 side of the fence), but I did some of my first color computer programming on them. Technology has not always been met with open arms, and I still chuckle remembering the day we came into the computer lab and found someone had stabbed a pencil into the computer, like a dagger.
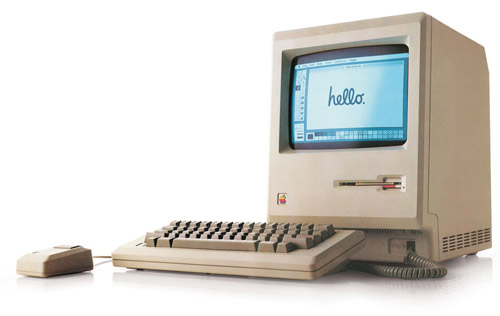 In college, I was fortunate to be right at the front of the revolution of personal computing when Jobs turned out the very first Mac. It was absolutely revolutionary. In one year we went from typewriters to Word processing. The simple Windows interface with an intuitive design was extremely simple for us college kids to pick up. It certainly put my TRS-80 to shame. It all seems very stone age now: the original Mac systems had no hard drive so everything was run from floppy disks (insert one for Word Processing, then swap it out to insert another to save the file). And all in just 128K of memory.
In college, I was fortunate to be right at the front of the revolution of personal computing when Jobs turned out the very first Mac. It was absolutely revolutionary. In one year we went from typewriters to Word processing. The simple Windows interface with an intuitive design was extremely simple for us college kids to pick up. It certainly put my TRS-80 to shame. It all seems very stone age now: the original Mac systems had no hard drive so everything was run from floppy disks (insert one for Word Processing, then swap it out to insert another to save the file). And all in just 128K of memory.
As my senior project, I went back to the Apple II (by then a relic in college library), and wrote assembly code for booting and saving data to a floppy disk. Not particularly exciting, but I cut my teeth on machine instructions and low-level programming. I also did some my first hardware hacking with the Apple II, using it in a club science project to control and display a model train layout.
The next huge experience with Steve Jobs was the birth of the World Wide Web. My wife was in graduate school at the time when I learned of a new program called Mosaic, that was changing the way we accessed data online. Up until then, almost all online access was via dial up connections to bulletin board systems (think forums and file downloads). Mosaic was the first widely available web browser, and later become Netscape. I can still remember going into the graduate school to use their high-speed network on an Apple computer to download Mosaic for my home PC (so for even a diehard PC guy like me, it was the Mac that opened the door to the web).
 We purchased our first Mac during those graduate school years. It was a Mac IIci, considered one of the first real workhorse Macs. It had a decent amount of memory and even a hard drive, and yes, cost a small fortune (we took a loan out!). My wife wrote her entire dissertation on that computer (and printed out on a HP Laserjet that we still use today!).
We purchased our first Mac during those graduate school years. It was a Mac IIci, considered one of the first real workhorse Macs. It had a decent amount of memory and even a hard drive, and yes, cost a small fortune (we took a loan out!). My wife wrote her entire dissertation on that computer (and printed out on a HP Laserjet that we still use today!).
Like Steve, there was a number of years after that where I wasn’t involved in Apple products. My world was filled with mainframes and minicomputers, and lots of PCs. The Mac line-up seemed to flounder with the Mac OS 8 and 9 operating systems, and their designs weren’t drawing a huge following.
 Jobs came back to me again roughly ten years ago when a person from our skiing community contacted me about problems with their PowerBook G3. The computer had died and the local repair technicians told them the data was a total loss. While I had had no recent experience with Mac systems, I offered my services. Working with that PowerBook gave me a renewed confidence in my tech skills as I was able to access the hard drive and recover all of the client data. That experience led to an every growing business of technical support and guidance, and eventually this web site.
Jobs came back to me again roughly ten years ago when a person from our skiing community contacted me about problems with their PowerBook G3. The computer had died and the local repair technicians told them the data was a total loss. While I had had no recent experience with Mac systems, I offered my services. Working with that PowerBook gave me a renewed confidence in my tech skills as I was able to access the hard drive and recover all of the client data. That experience led to an every growing business of technical support and guidance, and eventually this web site.
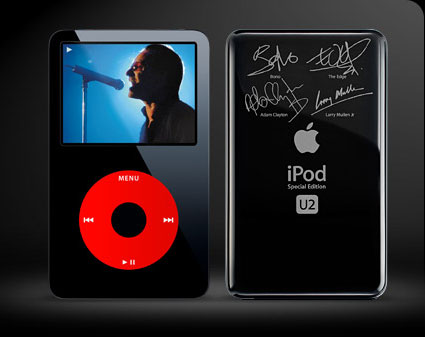 I can still remember working with another client on Jobs first step outside the formal computer world, the iPod. I assisted the client with the set up of their brand-new iPod U2 special edition, a black and red 20GB unit pre-loaded with the entire U2 collection. An impressive device, and more so, a remarkable bit of foresight and salesmanship for Jobs to bring iTunes to reshape and dominant the music industry.
I can still remember working with another client on Jobs first step outside the formal computer world, the iPod. I assisted the client with the set up of their brand-new iPod U2 special edition, a black and red 20GB unit pre-loaded with the entire U2 collection. An impressive device, and more so, a remarkable bit of foresight and salesmanship for Jobs to bring iTunes to reshape and dominant the music industry.
 My revolutionary experience continued with Jobs’ mega-earthquake, the iPhone. I can still recall emailing friends to let them know this phone was absolutely a game changer, heads and tails above everything else on the market. The product almost immediately led to the collapse of Nokia and the counterstrike from Google, the Android phones.
My revolutionary experience continued with Jobs’ mega-earthquake, the iPhone. I can still recall emailing friends to let them know this phone was absolutely a game changer, heads and tails above everything else on the market. The product almost immediately led to the collapse of Nokia and the counterstrike from Google, the Android phones.
 In recent months, I’ve been back in the Jobs neighborhood again, this time reviewing and purchasing used MacBook Pro laptops for a number of clients. The solid laptop construction and beautifully integrated OS X software still has all the hallmarks of Steve Jobs quest for perfection and clean design.
In recent months, I’ve been back in the Jobs neighborhood again, this time reviewing and purchasing used MacBook Pro laptops for a number of clients. The solid laptop construction and beautifully integrated OS X software still has all the hallmarks of Steve Jobs quest for perfection and clean design.
These days I see Jobs handywork everywhere, from reading the morning news on an iPad to listening to some tunes on the iPod Touch while working in the kitchen.
I will always look back very fondly on my days with Steve Jobs. I know I have lived through the times with one who clearly will be viewed in history as a major founding father for much of the consumer technology progress of the last 40 years. And I look hopefully for another person to step up and lead the way as clearly as Jobs did.
Bruce Adelsman
October 2011